UltraISO 9.7.2.3561 Crack is a powerful software to create, modify and convert ISO image files used for optical disk authoring.It is specially designed for Windows. With a standard interface, UltraISO is easy to use. It supports and can convert almost all image file formats to the ISO standard. Ultraiso key generator free download.
- Asymmetric Function That Generates New Keys Everytime It Runs Lyrics
- Asymmetric Function That Generates New Keys Everytime It Runs On Computer
- Asymmetric Function That Generates New Keys Everytime It Runs On Video
- Asymmetric Function That Generates New Keys Everytime It Runs On Love
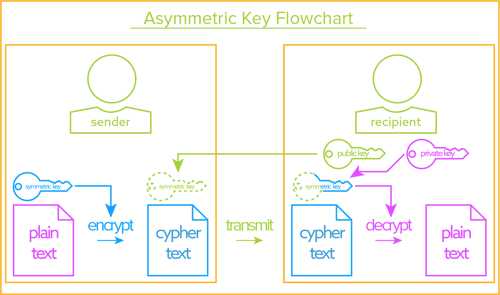
Public-key cryptography, or asymmetric cryptography, is a cryptographic system that uses pairs of keys: public keys, which may be disseminated widely, and private keys,which are known only to the owner. The generation of such keys depends on cryptographic algorithms based on mathematical problems to produce one-way functions. Effective security.
Asymmetric encryption
Keys
Asymmetric encryption requires pairs of public/private keys that match such that it is infeasible to guess the private key from the public key. Asymmetric keys have a special structure based on large prime numbers. This structure makes keys easier to guess meaning that asymmetric keys need to be much longer than a symmetric key to be secure.Symmetric keys can be any string as they have no special properties. As such, they can be generated in a random fashion that makes them more difficult to guess. A symmetric key of 256 bits may be more secure than a far larger asymmetric key.Distribution
Symmetric keys need to be distributed to partners in order to communicate using encryption. This presents a security challenge when dealing with a large number of communication endpoints. Asymmetric encryption solves this problem with public keys that can be published securely to anyone.Speed
Asymmetric encryption relies on algorithms that are far slower than symmetric encryption.Asymmetric + Symmetric

Keys
Asymmetric encryption requires pairs of public/private keys that match such that it is infeasible to guess the private key from the public key. Asymmetric keys have a special structure based on large prime numbers. This structure makes keys easier to guess meaning that asymmetric keys need to be much longer than a symmetric key to be secure.Symmetric keys can be any string as they have no special properties. As such, they can be generated in a random fashion that makes them more difficult to guess. A symmetric key of 256 bits may be more secure than a far larger asymmetric key.Distribution
Symmetric keys need to be distributed to partners in order to communicate using encryption. This presents a security challenge when dealing with a large number of communication endpoints. Asymmetric encryption solves this problem with public keys that can be published securely to anyone.Speed
Asymmetric encryption relies on algorithms that are far slower than symmetric encryption.Asymmetric + Symmetric
It is common to use asymmetric encryption to exchange symmetric keys and then communicate with symmetric encryption. This approach gains the distribution advantages of the asymmetric approach and the speed and enhanced key strength of symmetric encryption.Data Encryption
Local applications of encryption such as encrypting data is storage is typically achieved with symmetric encryption.| Asymmetric Encryption vs Symmetric Encryption | ||
| Asymmetric Encryption | Symmetric Encryption | |
| Definition | Encryption based on public/private key pairs that allows anyone to send an encrypted message to a receiver that only the receiver can read. | Encryption based on private keys. |
| Advantages | Distributing keys over the internet and other large networks. | SpeedKeys can be fully random |
Cryptography
Derrick Rountree, in Security for Microsoft Windows System Administrators, 2011
Navicat premium 12 key generator. Function offset = +0x00ec9868 Keyword offset = +0x0263fd60 std::string::append(const char.) RVA = 0x14b726. Ready to apply.
Asymmetric Encryption
Asymmetric encryption is also referred to as public key encryption. In asymmetric encryption, both the encrypting and decrypting systems have a set of keys. One is called the public key, and another is called the private key. If the message is encrypted with one key in the pair, the message can be decrypted only with the other key in the pair. Parallels activation key free generator.
Asymmetric key algorithms are not quite as fast as symmetric key algorithms. This is partially due to the fact that asymmetric key algorithms are generally more complex, using a more sophisticated set of functions.
(The ' Load, save or delete a stored session ' helps you to set some connection without acknowledging all the details again and again.). https://dispacapan1973.mystrikingly.com/blog/putty-key-generator-download-for-windows-8.
Asymmetric Key Algorithms
Asymmetric Function That Generates New Keys Everytime It Runs Lyrics
Asymmetric key algorithms aren't as widely used as their symmetric counterparts. So we'll just go over two of the big ones: Diffie-Hellman and RSA.
Diffie-Hellman: The Diffie-Hellman algorithm was one of the earliest known asymmetric key implementations. The Diffie-Hellman algorithm is mostly used for key exchange. Although symmetric key algorithms are fast and secure, key exchange is always a problem. You have to figure out a way to get the private key to all systems. The Diffie-Hellman algorithm helps with this. The Diffie-Hellman algorithm will be used to establish a secure communication channel. This channel is used by the systems to exchange a private key. This private key is then used to do symmetric encryption between the two systems.
Asymmetric Function That Generates New Keys Everytime It Runs On Computer
RSA: It is the Rivest Shamir Adelman algorithm. RSA was developed in 1978. RSA was the first widely used asymmetric algorithms used for signing and encryption. It supports key lengths of 768 and 1,024 bits. The RSA algorithm uses a three-part process. The first part is key generation. The keys used in the RSA algorithm are generated using mathematical operations based on prime numbers. The second part of the process is encryption. This encryption is done using one of the keys in the key pair. The third part of the process is decryption. The decryption is done using the other key in the key pair.
